VAPT (Vulnerability Assessment and Penetration Testing)
🔐 VAPT (Vulnerability Assessment & Penetration Testing) in 30 Days*
⚙️ Secure Your Digital Assets & Build Unshakable Trust
- Identify and eliminate hidden vulnerabilities in your systems, networks and applications
- Simulate real-world cyber-attacks to test your defences before malicious actors do
- Achieve compliance with global standards (e.g., ISO/IEC 27001, GDPR, SOC 2) and regulatory mandates
- Demonstrate to clients and stakeholders your commitment to cybersecurity and risk-resilience
- 100 % guarantee — we don’t get paid until you’re certified
🎁 Limited Time: Get a Free 2-Hour Training & Awareness Session with Certificates — for a Group of 5!
Introduction: Understanding What is VAPT and its Significance in Cybersecurity
In today’s digital age, cybersecurity has become a critical concern for organizations across various industries. With the increasing number of cyber threats and data breaches, it has become imperative for businesses to adopt robust measures to safeguard their sensitive information. One such essential practice is VAPT full form is Vulnerability Assessment and Penetration Testing , a process that plays a crucial role in ensuring the security of an organization’s IT infrastructure.
VAPT involves identifying vulnerabilities in an organization’s systems, networks, and applications through comprehensive assessments. These assessments are performed by skilled cybersecurity professionals who simulate real-world attacks to identify potential weaknesses that malicious actors could exploit. By conducting VAPT, organizations can proactively address these vulnerabilities before they can be exploited by cybercriminals.
The significance of VAPT cannot be underestimated in the realm of cybersecurity. It provides organizations with valuable insights into their security posture and helps them identify areas that require immediate attention. Moreover, VAPT is often mandated by regulatory bodies and industry standards such as ISO 27001 compliance, making it an essential component for businesses striving to maintain data integrity and protect customer trust.
A VAPT report is a comprehensive examination of the vulnerabilities found during the security test.
In this section, we will delve deeper into the concept of VAPT and explore its meaning and significance in securing IT infrastructures against evolving cyber threats. We will also discuss various use cases and best practices related to VAPT implementation within organizations.
🔐 Benefits of VAPT Certification
🧩 Security Assurance
Helps build structured and proactive security processes to identify, assess, and remediate vulnerabilities.
⚖️ Regulatory Compliance
Meets national and international cybersecurity requirements by performing formal VAPT assessments.
🛡 Risk Mitigation
Reduces the risk of data breaches, system downtime, and reputational damage.
🌐 Client & Stakeholder Trust
Boosts confidence among partners, customers and stakeholders by showing your IT estate is continuously audited and improved.
💡 Cost Efficiency
Avoids costly remediation after incidents, reduces insurance and compliance overheads, and lowers incident-response costs.
🏅 Market Differentiation
Positions your organisation as a secure, trustworthy, and globally compliant cybersecurity-ready business.
📑 Table of Contents – VAPT (Vulnerability Assessment & Penetration Testing)
- Introduction: What is VAPT?
- Why Vulnerability Assessment & Penetration Testing (VAPT) is Crucial for IT Industries?
- Apply for VAPT Certification
- Benefits of VAPT Testing in IT Industries
- Types of VAPT Services: White Box, Black Box, Grey Box
- VAPT Process & Methodology Overview
- ISO 27001 Compliance and VAPT Relationship
- PDCA Cycle – VAPT
- VAPT Frequently Asked Questions (FAQs)
VAPT for IT Industries and ISO 27001 Compliant Organizations
Why Vulnerability Assessment and Penetration Testing (VAPT) is Crucial for IT Industries?
Data breaches and cyber threats are becoming increasingly prevalent, Information Technologies Industries must prioritize vulnerability assessment and penetration testing (VAPT) as part of their security measures.
Vulnerability assessment involves identifying potential weaknesses in a network or system that could be exploited by hackers. By conducting regular assessments, IT industries can proactively identify and address vulnerabilities before they are exploited, thus minimizing the risk of data breaches and unauthorized access.
Penetration testing takes the assessment a step further by simulating real-world attacks to evaluate the effectiveness of existing security controls. This process helps identify any gaps in network security, allowing organizations to strengthen their defenses and mitigate potential risks.
Implementing VAPT not only protects sensitive data but also safeguards an organization’s reputation. A single data breach can have severe consequences, including financial loss, damage to brand reputation, and legal implications. By investing in comprehensive IT security assessments, companies demonstrate their commitment to protecting customer information and maintaining trust.
Furthermore, compliance with industry regulations such as GDPR (General Data Protection Regulation), ISO 27001, CMMI, SOC-1 and SOC-2 often requires organizations to conduct regular VAPT assessments. Failure to comply with these regulations can result in hefty fines and legal penalties.
Which of the following is Best Used with Vulnerability Assessments?
White box testing
The Vapt test fully comprehends the system’s functionality, including its source code, documents, internal structures, and workflow. Because of this transparency, tests can be run much more quickly, and the results can be thoroughly analyzed.
Black box testing
The tester in this instance is unaware of the functionality, codes, architecture, and structures. The tester simulates a hostile incursion and evaluates the system’s reactions to imitate real malicious attacks.
Gray box testing
Gray box testing strikes a balance between the two by giving the tester some knowledge about the application. The goal is to find configuration-related issues.
Benefits of VAPT testing in IT Industries:-
In the subject of cybersecurity, particularly within IT enterprises, vulnerability assessment and penetration testing (VAPT) are crucial elements. Here are some key benefits:
- Identifying Weaknesses: VAPT assists enterprises in identifying vulnerabilities in their systems, networks, and applications Before attackers do, this proactive approach enables the quick repair or mitigation of these weaknesses.
- Risk Assessment: VAPT offers a thorough evaluation of the possible effects that exploits might have on the system. By concentrating on high-risk vulnerabilities, it can help prioritize security efforts.
- Regulatory Compliance: The periodic VAPT is mandated by laws in several businesses. Through the execution of these tests, organizations can comply with legal obligations, avoid penalties, and showcase to stakeholders their commitment to security.
- Preventing Financial Loss: Due to data breaches, ransomware attacks, etc., cyberattacks can cause substantial financial loss. Such situations can be avoided through VAPT, protecting the company from significant financial loss.
- Protecting Customer Trust: Businesses may keep their customers’ trust by guaranteeing the security of their systems. A secure business is more likely to keep its clients and lure in new ones.
- Creating Security Awareness: Additionally, VAPT aids in instructing the organization’s workforce about the significance of security precautions and how to react in the event of a breach.
- Enhancing Business Continuity: Businesses can avoid disruptions brought on by cyberattacks, ensuring smooth operations and business continuity, by discovering and addressing vulnerabilities.
- Informed Decision Making: The thorough reports produced by VAPT offer insightful information that helps guide decisions regarding IT investments and security protocols.
Since new vulnerabilities might develop over time as technology and threat landscapes change, VAPT should be a continuous process rather than a one-time occurrence.
ISO standards applicable to the IT industry
ISO 9001 Quality Management Systems (QMS)
ISO 9001 helps in the implementation of a quality management system in an organization. This standard can be applied to any organization irrespective of the sector that they belong to. For IT industries, it helps in ensuring the quality of services.
ISO 14001 Environmental Management Systems (EMS)
Every industry, including the IT sector, is required to demonstrate its commitment to a sustainable environment. For that purpose, ISO 14001 certification can act as proof of your commitment to the environment as well as compliance with related regulations.
ISO 45001 Occupational Health and Safety Management System (OH&SMS)
The occupational safety of the employees has a direct relation with productivity. With ISO 45001 certification, an IT company can demonstrate its commitment to providing a safe work environment for its staff.
ISO 27001 Information Security Management System (ISMS)
ISO 27001 standard helps in the implementation of Information security management systems that ensure the safety and privacy of data stored within the organizations. The IT sector deals with a huge amount of online data that needs to be protected against any breach or loss.
ISO 22301 Business Continuity Management System (BCMS)
This standard helps in the implementation of a Business Continuity Management System in an organization and helps them in identifying and eliminating any risk that can affect the continuity of business.
ISO 27701 Privacy Information Management System (PIMS)
This standard is a data privacy extension of ISO 27001 certification and helps organizations with their GDPR compliance. It is also called PIMS (Privacy Information Management System) and it sets a framework for Personally Identifiable Information (PII) controllers and processors for data management.
CMMI LEVEL-3 and LEVEL-5
The Capability Maturity Model Integration also known as CMMI provides a framework for the organisation to enhance its services and quality of products. It focuses on leveraging your current business strategy, identifying problem areas, developing tools, and creating models for current and future processes.
SOC 1 and SOC 2:
SOC stands for System and Organisation Controls. SOC compliance ensures that an organisation follows best practices related to protecting its customers’ data before entrusting a business function to that organisation. These best practices are in the areas of finance, security, processing integrity, privacy, and availability.
In conclusion, VAPT plays a crucial role in safeguarding IT industries against evolving cyber threats. By proactively assessing vulnerabilities and conducting penetration tests, organizations can enhance their network security measures, reduce the risk of data breaches, protect sensitive information, maintain regulatory compliance, and ultimately ensure the longevity of their business operations.
PDCA Cycle
- Plan – to think that what do we need to achieve in our organization
- Do – to execute a planned action which will help us achieve the required objective
- Check – monitor against the standards) (policies, objectives, requirements)
- Action – finally implementing what has been rechecked.
VAPT Frequently Asked Questions (FAQs)
Answer:
VAPT combines Vulnerability Assessment and Penetration Testing—two related cybersecurity processes that identify, analyze, and address security vulnerabilities in systems, networks, applications, and IT infrastructure. It is an essential part of a strong cybersecurity program.
Answer:
VAPT helps businesses proactively detect security weaknesses, prevent cyberattacks, reduce data-breach risks, and avoid financial losses. It strengthens the organization’s overall security posture and builds a more secure IT environment.
Answer:
Vulnerability Assessment uses automated tools to identify and rank security weaknesses.
Penetration Testing simulates a real-world cyberattack to exploit vulnerabilities, determine actual impact, and provide deeper security insights.
Together, they give a complete picture of potential security risks.
Answer:
VAPT should be performed regularly—ideally annually, and also after major system upgrades, new deployments, or significant changes. Frequent testing ensures continuous protection against emerging threats.
Answer:
VAPT identifies vulnerabilities such as:
Unpatched operating systems or software
Misconfigurations
Weak or reused passwords
Insecure network protocols
Inadequate access controls
Poor coding practices in applications
Answer:
The duration depends on the size and complexity of the environment. A typical assessment may take a few days to several weeks based on scope, number of assets, and testing depth.
Answer:
Yes. VAPT can assess:
Web applications
Mobile applications
APIs
Network infrastructure
Cloud environments
Servers and endpoints
It improves the overall security of the organization.
Answer:
Yes. VAPT aligns with key standards such as:
ISO 27001
GDPR
HIPAA
PCI DSS
SOC requirements
It helps organizations meet regulatory obligations and demonstrate security compliance.
Answer:
A standard VAPT process includes:
Scoping
Vulnerability scanning
Manual testing
Exploitation of weaknesses
Analysis and validation
Reporting with remediation steps
Answer:
Select a provider based on:
Industry experience
Certified security professionals (CEH, OSCP, CISSP)
Clear testing methodology
Strong reputation and client reviews
Compliance knowledge
Transparent reporting and remediation support
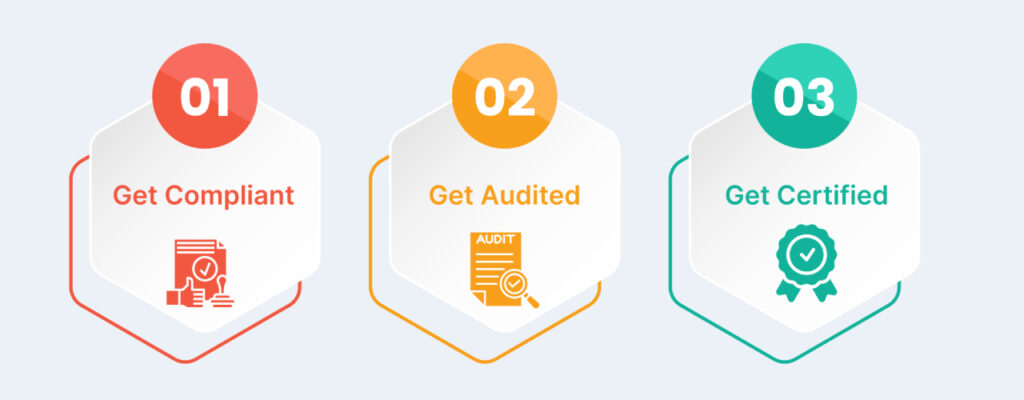
CERTIFICATION PROCESS
Ready to Get ISO Certified?
Join 500+ Global Companies that have Successfully Achieved ISO Certification with Us.
Missing Something?
We’re here to help you find exactly what you need—just let us know, and we’ll guide you in the right direction.