PCI DSS Compliance
💳 PCI DSS Compliance in 30 Days*
🔐 Secure Payment Card Data & Strengthen Business Trust
- Protect card‐holder data by implementing robust security controls across systems, applications and networks
- Comply with global payment-card industry requirements and avoid heavy fines and brand damage
- Demonstrate to clients and partners that you take payments & data seriously
- Build market recognition as a secure, trusted processor or merchant
- 100 % guarantee — we don’t get paid until you’re certified
🎁 Limited Time: Get a Free 2-Hour Training & Awareness Session with Certificates — for a Group of 5!
Introduction: What is PCI DSS Compliance and Its Importance
Since online transactions are now widespread, it is crucial to ensure that these transactions are secure. This is when adhering to PCI DSS is necessary. The Payment Card Industry Data Security Standard (PCI DSS) is a set of payment security requirements that require all sellers to accept, store, process, and transmit cardholder data (commonly known as your customers’ credit card information) safely and securely during a credit card transaction.
PCI DSS compliance is critical for every business that accepts credit or debit card payments. It assures that firms use strong security measures to prevent unwanted access to customer information during payment processing. Companies that abide by these guidelines may safeguard their client’s financial and personal data from possible hacks or breaches.
It is impossible to overstate the importance of PCI DSS compliance. Serious consequences for noncompliance include costly fines, damage to one’s reputation, and even loss of clientele. Contrarily, adhering to these standards shows a dedication to upholding the highest level of security for confidential client information.
Businesses may take proactive measures to secure payment operations and foster customer trust by learning what PCI DSS compliance means and why it matters.
💳 Benefits of PCI DSS Compliance
🛡️ Data Protection Assurance
Establishes structured controls to protect card-holder data from theft, misuse or exposure.
⚖️ Regulatory & Payment-Brand Compliance
Fulfills major card-brand (e.g., Visa, MasterCard, Amex) requirements and reduces risk of fines, penalties or being denied card-processing.
🤝 Trust & Customer Confidence
Boosts confidence among customers and partners by showing you handle payments with the highest standards of security.
💼 Operational Efficiency & Cost Savings
Reduces risk of breaches and associated costs (remediation, legal, reputational loss) by proactively managing payment-data processes.
🧩 Baseline for Other Standards
Provides a strong security foundation that helps you align with other frameworks like ISO 27001, SOC 2 or GDPR compliance.
🌍 Market Differentiation
Positions your organisation as a secure, compliant merchant or service-provider — enhancing your reputation and competitive edge.
📑 Table of Contents – PCI DSS Compliance & Certification
PCI DSS Compliance levels
PCI Compliance is separated into four distinct tiers based on annual card transaction volume (credit, debit, and prepaid). In the event of a data breach, a merchant may be required to enhance their level of compliance.
level 1 merchants
This level includes merchants who complete over 6 million transactions in 12 months across all channels. (card present, card not present, and eCommerce). It also includes global merchants who process 6 million transactions across all of their territories, which may need the entire firm to comply.As a level 1 merchant, you must:
Annually submit a Report on Compliance (ROC) to a Qualified Security Assessor (QSA).Complete quarterly network scans by an ASV.
Fill out the Compliance Attestation Form.
Level 2 Merchants
This class includes retailers who process between 1 and 6 million transactions each year via all channels (card present, card not present, and eCommerce).As a level 2 merchant, you must:
Completing an Annual Self-Assessment Questionnaire (SAQ) is required.An ASV should perform a quarterly network scan.
Fill out the Compliance Attestation Form.
Level 3 Merchant
This class includes merchants who execute 20,000 to 1 million transactions through eCommerce processing techniques in 12 months.As a level 3 merchant, you must:
Completing an Annual Self-Assessment Questionnaire (SAQ) is required.An ASV should perform a quarterly network scan.
Fill out the Compliance Attestation Form.
Level 4 Merchants
This level includes merchants who conduct up to 1 million transactions per year across all channels (card present, card not present, and eCommerce) but do not execute more than 20,000 transactions per year via eCommerce. Similarly, a merchant who processes fewer than 20,000 eCommerce transactions per year may be eligible for level 4 certification.As a level 4 merchant, you must:
Annual Self-Evaluation QuestionnaireAn ASV should perform a quarterly network scan.
Fill out the Compliance Attestation Form. c v0062
PCI DSS Requirements
- Protect your cardholder data by installing and maintaining firewalls.
Firewalls are your first line of protection to prevent data breaches. Firewalls are designed to keep your network safe from harmful malware and unauthorized access, they regulate traffic based on the parameters that you choose for your company.
Software firewalls are systems that defend against internal dangers such as malware infections obtained through phishing scams. Compared to physical firewalls, software firewalls are less costly and easier to manage.
Hardware firewalls are physical devices that secure and segment your network, but they must be properly configured and maintained regularly. To keep your firewall settings effective, you should evaluate them every six months.
Firewall software should be installed on any device (business or employee-owned) that connects to the internet or is used to access cardholder data. - Never Use Your Password Management Tools with Default Settings
The default configurations are general and simple to figure out. The majority of servers, mail suites, wireless printers, firewalls, internet routers, etc. frequently have these settings. This security criterion requires you to create a “strong” password manually and to change it regularly. It also lists all endpoints and cloud assets that could be compromised. - Safeguard the Data
Advanced hashing techniques, tokenization methods, or other encryption methods that fulfil global standards must be used to encrypt user data. To do so effectively, providers must have insight into all existing resources that contain user information, including data kinds such as shared spreadsheets, logs, and underutilized databases, all of which can become security concerns. - Encrypt the data that is transmitted by cardholders across public, open networks.
Cardholder data must always be encrypted when transmitted over public or open networks to prevent hacking. To protect against theft or infiltration, you must utilize safe encryption technology along with proper security standards. Personal account numbers should never be sent via communications services like chat, IM, SMS, or email. - Secure your anti-virus software
Regular updates are necessary to provide malware protection on all devices that have anti-virus software installed. Occasionally, though, the attack strikes the antivirus software itself first. Keeping your desktop, laptop, mobile, and other endpoint anti-virus software up to date enables you to identify malware and take the appropriate precautions to be safe. - Provide and manage safe software and systems
Ensure that you have a strategy in place to manage routine patch management. Patch updates are routinely applied to operating systems, firewalls, web browsers, and application software.
Ensuring data security requires prompt implementation of security upgrades. One month after release, important patches must be installed to comply with Payment Card Industry Data Security Standard (PCI DSS) PCI DSS. - Access Control Based on Roles
To avoid data exposure within the company, credit card information should only be available to those who need to know. Every person who has access to such important information must be recorded. They should be able to carry out their duties and responsibilities with the support of this list, which should include their designations. - Unique Access
Before giving a user access to system components and/or cardholder data, you must assign them a unique ID. Specific user IDs provide accountability by allowing any behaviour related to the usage of cardholder data functions to be linked back to a specific known user. It is resolved through the implementation of robust access control methods. - Limit physical access to cardholder data
Cardholder data cannot be kept in a publicly accessible or open environment. You need to limit physical access to data to prevent employees, consultants, and contractors from stealing it while they are on your property. Reduce the chance of data exposure by using ID badges to identify guests or temporary employees.
Any tangible object that grants access (such as keys or access cards) needs to be disabled or returned upon termination. Regularly train your employees on security protocols. - Monitoring for anomalies continuously
Look for irregularities that could breach your security measures daily. Then, execute audits and keep a 365-day audit trail of all security reports. Working with security experts such as SIEM, CSPM, and CASB providers can assist you in accomplishing this efficiently. - Conduct routine tests of security procedures and systems
Regular system testing, in addition to basic system monitoring, keeps your business one step ahead of security threats and weaknesses. Preventative testing of system controls will help you make sure your security measures are both compliant and effective.
You should conduct extra testing in addition to standard testing whenever you install new software or modify system parameters. Penetration tests and vulnerability scans help to preserve system integrity by spotting possible attacks.
Depending on your infrastructure and business size, different scan and test frequencies are necessary. - Keep an information security policy in place that covers risk assessments for all employees
Your staff members need to be aware of their responsibilities and roles in upholding the relevant security requirements. To maintain compliance with PCI DSS rules, your organization needs to take cardholder data security very seriously.
Keeping up a robust security policy eliminates uncertainty in compliance requirements. It establishes standards for worker performance in terms of risk management. Every year, you should evaluate and update your security policy to consider any changes to the environment or systems.
An annual risk assessment is also necessary to pinpoint vulnerable areas and important assets.
Benefits of implementing PCI DSS
- PCI Compliance certifies that your systems are secure and that your clients can entrust you with their sensitive credit card information. Customer trust leads to repeat business.
- Requirements for PCI DSS reduce the possibility of data breaches and unwanted access to private credit card information. This protects the company’s financial resources, strengthens its security defences against new threats, and increases consumer trust in sharing sensitive payment card information.
- Businesses that optimize their processes and adhere to PCI DSS rules reduce the risk of data breaches and the costs that come with them. This fosters a more productive and long-lasting corporate environment
- Vulnerabilities in payment card systems can be found and fixed more quickly when PCI DSS requirements are followed. Through this, businesses may significantly reduce the likelihood of security lapses, financial losses, and harm to their reputation.
- Many large businesses look for PCI-compliant vendors. Thus, it facilitates commercial company expansion.
Drawbacks of Being PCI Non-Compliant
If you or your organization handles credit card transaction data, you have to comply with PCI standards. Additional fines and penalties, as well as the inability to collect credit card information going forward, could arise from a data breach. Banks and payment processors may reject you if you don’t follow PCI compliance. Revenue loss and a damaged reputation for the brand could result from this.
The consequences for noncompliance vary according to the type of PCI data security event or breach. In addition, people whose information is thought to have been hacked should receive a written notice warning them to be on the lookout for fraudulent transactions.
Conclusion
In conclusion, companies handling cardholder data must do a PCI DSS compliance audit. You may create a safe payment environment, safeguard the information of your clients, and reduce the possibility of data breaches by using the procedures described in this article. Making PCI DSS compliance a top priority can help you win over clients’ trust and maintain the long-term viability of your company.
PCI Frequently Asked Questions (FAQs)
Answer:
PCI DSS (Payment Card Industry Data Security Standard) is a global security framework that ensures companies accepting or handling card payments protect cardholder data through strict security controls.
Answer:
Any business—small or large—that accepts, processes, stores, or transmits credit/debit card information must comply with PCI DSS requirements.
Answer:
It helps prevent data breaches, protects cardholder information, maintains customer trust, avoids financial penalties, and ensures secure payment operations.
Answer:
Organizations must identify their cardholder data environment, conduct vulnerability scans, fix gaps, complete a Self-Assessment Questionnaire (SAQ) or undergo a QSA audit, and submit compliance reports.
Answer:
PCI DSS requires annual assessments and quarterly vulnerability scans to maintain compliance and ensure ongoing security.
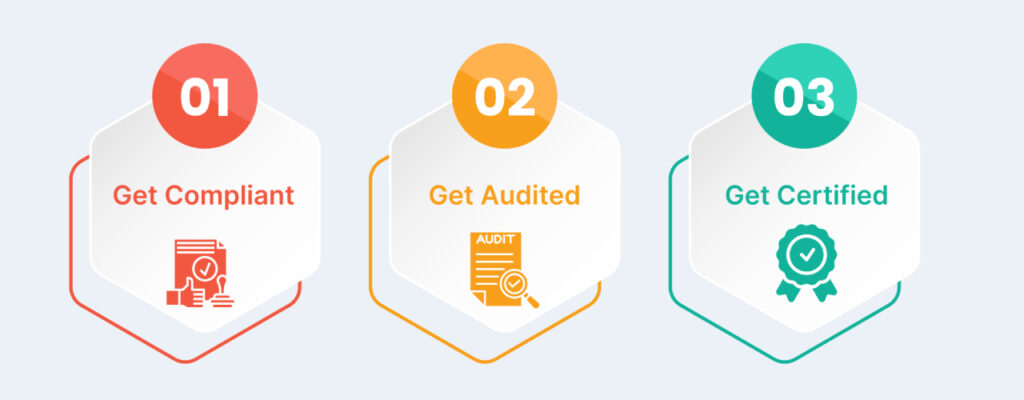
CERTIFICATION PROCESS
Ready to Get ISO Certified?
Join 500+ Global Companies that have Successfully Achieved ISO Certification with Us.
Missing Something?
We’re here to help you find exactly what you need—just let us know, and we’ll guide you in the right direction.