The ISO/IEC 27001:2013 Certification is an international ISO 27001 standard for Information Security Management System. It defines Security controls that aim to address the risks related to cyber security and implement an effective information security system. Annex A Controls of ISO 27001 consists of 114 security controls.
Annex A Controls
Annex A of ISO 27001 contains 114 security controls grouped into 14 control categories, and not all controls are mandatory. The selection of controls depends on the organization’s risk assessment. ISO 27001 Certification follows a risk-based approach and focuses on identifying the risk to its information security and selecting the appropriate controls to eliminate them.
ISO/IEC 27001:2013 Certification outlines ISO 27001 Annex A controls, also known as ISO 27002.
What is the difference between ISO 27001 and ISO 27002 Certification?⮯
Annex A controls of ISO 27001 Certification is one of the most well-known annex of ISO standards. It is a list of controls that aim to protect and strengthen the information security assets of the organization. ISO 27001 gives a general idea about these controls in one sentence.
The International organization for standardization published ISO 27002 certification to provide an extensive description on implementing these controls. It works on the same lines as ISO 27001 but has more details on controls.
List of ISO 27001 Annex A controls ⮯
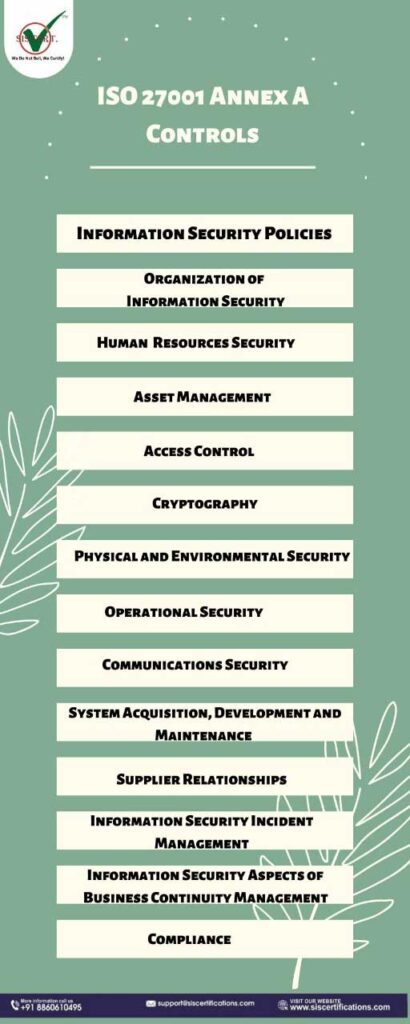
Annex controls of ISO 27001 are grouped into 14 domains. These are:
- Information Security Policies
- Organization of Information Security
- Human Resources Security
- Asset Management
- Access Control
- Cryptography
- Physical and Environmental Security
- Operational Security
- Communications Security
- System Acquisitions, Development and Maintenance
- Supplier Relationships
- Information Security Incident Management
- Information Security Aspects of Business Continuity Management
- Compliance
A Guide to ISO 27001 Annex A controls ⮯
The Security controls allow an organization to manage its information security assets and prepare against cyber threats. It enables an organization to avoid regulatory fines due to cyber-attacks, such as data breaches and malware. These controls cover specific topics and the purpose of these 14 controls is:
- Information Security Policies (2 controls) – It aims to provide direction and support to the management to implement information security. It helps organizations to formulate their information security policy based on the needs and requirements of the organization.
- Organization of Information Security (7 Controls) – This annex has seven controls divided into two sections which are Internal Organization and Mobile Device and Teleworking.
- Internal organization: It assigns roles and responsibilities to initiate and control the implementation of the Security management system. It aims to establish an efficient management framework to implement and maintain Information security practices.
- Mobile Device and Teleworking: It addresses the issues associated with remote working and the risk related to the use of mobile devices. It provides training and complies with regulations to access, process and store information remotely.
- Human Resources Security (6 controls) – These controls are divided into three sections. These are:
- Pre-employment requirements– A contractor needs to do appropriate background verification and state responsibilities in the employment contract to ensure information safety.
- Responsibilities during employment– It requires an organization to provide training to implement a disciplinary process to protect information security. Candidates need to be aware of their job responsibilities and update themselves.
- Termination and change of employment– It ensures to protect organization’s interest when candidates change or leave the organization.
- Asset Management (10 Controls) – These ten controls are grouped into three domains.
- Identification of Information Assets– It requires implementing an asset inventory, including its designated asset owners. The organization must implement and document controls associated with acceptable use.
- Information Classification– An organization must classify its information and assets accordingly and ensure adequate security measures.
- Media Handling– It prevents the unauthorized access, disclosure or destruction of information.
- Access Control (14 controls) – Access control is divided into four sections.
- Requirements of access control– It requires limiting access to information and information processing by implementing an access control policy.
- User access management– It aims to provide physical and virtual authorization to access the system and prevent unauthorized access to the employees.
- System and application access control– It prevents unauthorized access to the system and application.
- User Responsibility– It makes users responsible for safeguarding their information, such as PINs, passwords and other confidential information.
- Cryptography (2 controls) –
- It enables an organization to use cryptographic controls for proper data encryption to protect the confidentiality, authenticity and integrity of data.
- Physical and Environmental Security (15 controls) – The 15 controls under this control are divided into two domains.
- Prevents unauthorized access- It aims to protect against any disruption and interference that might occur to physical facilities. It protects against unauthorized access to an organization’s information and facilities.
- Prevent loss- It prevents loss, damage and theft of information and asset.
- Operational Security (14 controls) – Operational security control is divided into seven sections. It aims to establish adequate information processing facilities to ensure correct business operations. It monitors requirements for data backup and integrity of operational software and protects from malware and vulnerabilities to address them accordingly.
- Communications Security (7 controls) – It is divided into two sections.
- Network security management– It protects the three main principles of Information Security Management, such as Confidentiality, Availability and Integrity.
- Information transfer– It requires an organization to adopt transfer policy, procedures and controls while transferring data to third-party, organizations and customers.
- System Acquisitions, Development and Maintenance (13 controls) – It ensures that security remains an integral part of the information system and requires updating the existing information system to improve business operations.
- Supplier Relationships (5 controls) – It contains five controls divided into two groups and aims to improve the interaction between an organization and a third party.
- Information security in supplier relationships– It aims to protect the valuable assets and information that can be accessed by suppliers to mitigate risks.
- Supplier service development management– It requires maintaining the level of information security and service delivery mentioned in the agreement.
- Information Security Incident Management (7 controls) – It ensures information security events and weaknesses related to information security are communicated in a way that renders time to take corrective actions.
- Information Security Aspects of Business Continuity Management (4 controls) – Business continuity Management system is divided into two groups.
- Information security continuity– It embeds information security continuity in the organization’s continuity management systems. It avoids cyber-attacks and data breaches.
- Redundancies– It ensures availability of information processing facilities and information security business processes without disruptions even during incidents and crisis.
- Compliance (8 controls) – It provides a holistic approach to the organization and avoids non-compliance with laws, regulations, statute and any other security requirements.
Conclusion ✅
Annex A controls are also known as ISO 27002. ISO/IEC 27001:2013 follows a risk-based approach to identify risks associated with information security and formulate strategies to eliminate security threats. Annex A controls are part of ISO 27001 security controls, but it provides only a general idea. International organization for standardization developed ISO 27002 to provide an extensive description of these annex controls.
Enjoy Reading –
- Know about NEW and latest Version of ISO/IEC 27001:2022 Certification
- A Step by Step Guide to ISO 27001 Annex A Controls
- Why is ISO 27001 Important These Days?
- ISO 27001 प्रमाणन की तैयारी